
Overview
Definitely the most advanced and up-to-date cyber security training ever organized, taught by trainers who perform security audits and penetration tests on a daily basis!
This is a 3 day comprehensive technical awareness training for system engineers, network administrators, IT staff, security officers and all enthusiasts.
Students will attack servers, clients, wireless networks, mobile devices and even humans! You will perform lateral movement, sniff networks, crack passwords with custom wordlists, create malware, and hack web vulnerabilities like SQL injection.
But it's not all about the hacking stuff: students will learn the basic concepts of cyber security, counterattack techniques, how to implement secure network architecture concepts & systems design, and how to identify threat actors and remediate vulnerabilities.
► Register here for our next session on-site in Menen (HQ) on June 24/25/26.

Objectives
After completing our training course, students should possess the ability to assess their own infrastructure for security vulnerabilities, confirm false positives using penetration testing and ethical hacking techniques, and implement a defense-in-depth security strategy.
Students will be equipped with the knowledge and skills necessary to ensure NIS2 compliance within their company. Our training program is designed to empower participants in navigating and implementing the requirements of NIS2, enhancing their capabilities to contribute to a secure and compliant organizational environment.
We focus on methodologies and procedures, and not solely on software tools. This approach, combined with our realistic hands-on labs, sets MME's courses apart from others!
Students will also be prepared to pass the Certified Ethical Hacker (CEH) exam... with ease.
Price: 1695 EUR (*)
- Course materials and software
- Penetration testing distribution
- Access to our hacking lab (on-premise or through VPN)
- Breakfast, lunch, drinks and snacks (on-premise)
- Certificate of completion
(*) Via de KMO-portefeuille kunnen middelgrote ondernemingen 35% steun en kleine ondernemingen 45% steun ontvangen voor deze opleiding!

Available dates
Register >> 03/12/2025 - 05/12/2025 | 09:00 - 17:00 | Menen
Register >> 28/01/2026 - 30/01/2026 | 09:00 - 17:00 | Antwerpen, via Syntra AB
Register >> 18/02/2026 - 20/02/2026 | 09:00 - 17:00 | Menen
Register >> 11/05/2026 - 13/05/2026 | 09:00 - 17:00 | Antwerpen, via Syntra AB
Register >> 24/06/2026 - 26/06/2026 | 09:00 - 17:00 | Menen
Register >> 26/08/2026 - 28/08/2026 | 09:00 - 17:00 | Antwerpen, via Syntra AB
Register >> 09/09/2026 - 11/09/2026 | 09:00 - 17:00 | Menen
Register >> 09/12/2026 - 11/12/2026 | 09:00 - 17:00 | Menen
This training can also be organized on-site, at your preferred location!
In addition, the training can be booked as a 2-days private session (= fast-track).



Related
Topics
- Day 1
- Introduction to Kali Linux
- Active and Passive Recon
- Scanning and Enumeration
- Vulnerability Mapping
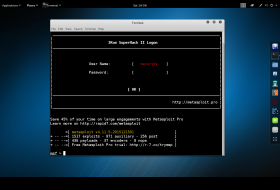
- Exploitation with Metasploit
- Man-in-the-Middle Attacks
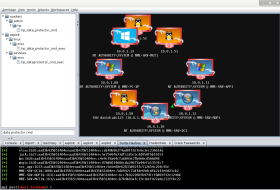
- Pivoting and Post-Exploitation
- Offline Password Cracking
- Day 2
- Hacking Wireless Networks
- Rogue Access Points
- Device: the WiFi Pineapple
- Online Password Attacks
- Creating Effective Wordlists
- Pass-the-Hash Techniques
- Token Impersonation
- Extracting Windows Credentials
- Happy Hunting with Armitage
- Day 3
- Social Engineering and Malware
- Client-Side Attacks
- Local Privilege Escalation
- Attacking Mobile Devices
- Introduction to Web Applications
- OWASP and its Top 10 Risks
- Web Application Scanners
- Exploiting SQL Injection
Requirements
- Your own laptop is required (!)
- Windows (pref), OS X or Linux
- Administrator privileges
- Access to BIOS settings
- Ethernet and USB interface
- Ability to disable AV and IPS
- VMware Player/Fusion installed
- Basic knowledge in TCP/IP
Contact us
Do not hesitate to contact us if you have any questions. We will gladly help you!
